Rooting Android is more popular today than it has ever been in the past. Today, some custom ROMs are updated more frequently than stock versions of Android. And of course, there are hundreds of new features and apps to access after rooting your Android.
But there are some important things to do before rooting your Android. Today, we’re going to list those things and show you how to have a safe and effective rooting experience:
Download only from trusted rooting sources
Rooting your Android gives you access to the very core features of your device. At the same time, your rooting kit/exploit kit needs to hack into your device to grant this access.
Most rooting kits are designed by programmers who find exploits simply for the challenge and the fame. These rooting kits are safe and are often free to download.
However, not all rooting kit programmers have benevolent goals. Some build root kits designed to brick your device, while others install malware and viruses on your device. Always download your root kits from trusted sources unless you want to brick your device (you don’t).
Trustworthy sources include:
And that’s about it. On the XDA Developers’ Forum, be sure to read through the thread to make sure other users have had success with a particular root exploit before you try it yourself.

Power up your Android to 100% battery life
I can’t believe this needs to be said, but it does. Rooting drains your phone’s battery life, but it doesn’t drain it at a crazy rate. That being said, there’s always some user who encounters a serious rooting problem because they didn’t listen to these instructions. Power up your phone to 100% before you attempt to root, and if you don’t have time to do that, then at least power it up to 50%, which should be enough.

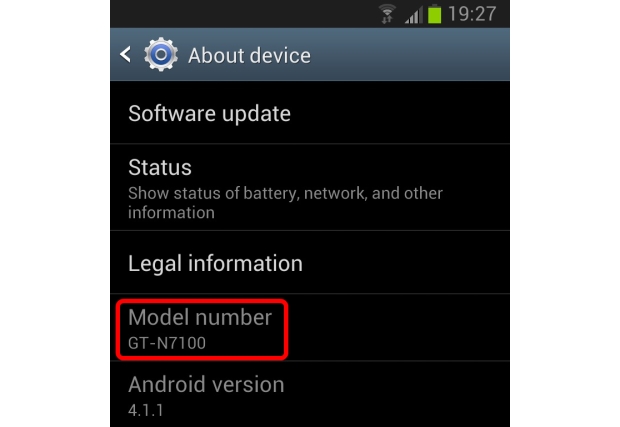
Know exactly which handset and model number you have
Let’s say you have a Galaxy S3. You find a Galaxy S3 rooting exploit for free online. “Great!”, you think. This will be perfect for me.
Unfortunately, that root exploit is only for the SGH-I337M model number with Verizon, and you’ve just bricked your phone.
Always be sure to download root exploits that are either:
-Designed for your specific phone
-Have been confirmed to work with your specific phone
Otherwise, you’re going to encounter some serious compatibility errors. To find your specific Android model number, look for About Phone under your Settings menu.
Backup your Android
Rooting an Android from any source comes with risks. The biggest risk is that you’ll brick your device and lose everything on it. That’s bad. That’s why you absolutely should back up your Android prior to rooting.
There are a number of reasons why a root could fail, including:
-You used a root kit for the wrong version of Android
-You used a root kit for the wrong model number of your Android phone or tablet
-Your battery died halfway through the rooting process

-The root kit is bad and enters a loop or encounters other errors
-You gave up halfway through and started crying
No matter why you’re rooting Android or which method you’re using, we highly recommend backing up your Android prior to rooting (you should probably be backing up your data on a regular basis anyway).
Let someone else be the test dummy
If you see a root exploit that doesn’t specifically cover your Android model number, then you probably don’t want to be the first to test that out. Unfortunately, some people like to try being the test dummy.
Just read through any root exploit kit thread at the XDA Developers’ Forum. There’s always someone who said “didn’t work…bricked my phone =(“ or something along those lines. Don’t be a test dummy and always wait for someone else to take the bullet. The internet is a big place and no matter how obscure your Android version may be, you’re not the only one in the world with that particular Android.
