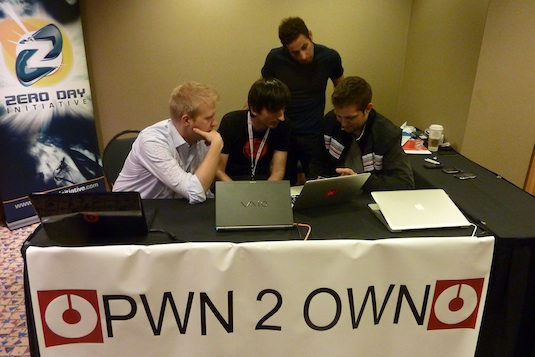
Pwn2Own is an annual hacking conference that brings together some of the world’s best exploit-seeking brains.
Every year, Pwn2Own makes headlines around the tech community. Devices that people thought were unhackable get hacked, and there’s always a surprising platform that withstands being attacked by some of the world’s best hackers.
This year’s Pwn2Own conference brought us some surprising results. Android and Windows Phone are making major headlines for withstanding a so-called “cyber-battering” from Pwn2Own attendees.
Two veteran security researchers from VUPEN were able to achieve partial “pwnage” of the two mobile OSes, which means they were able to control one aspect of each. However, neither was able to achieve full control.
Only one researcher attacked Windows Phone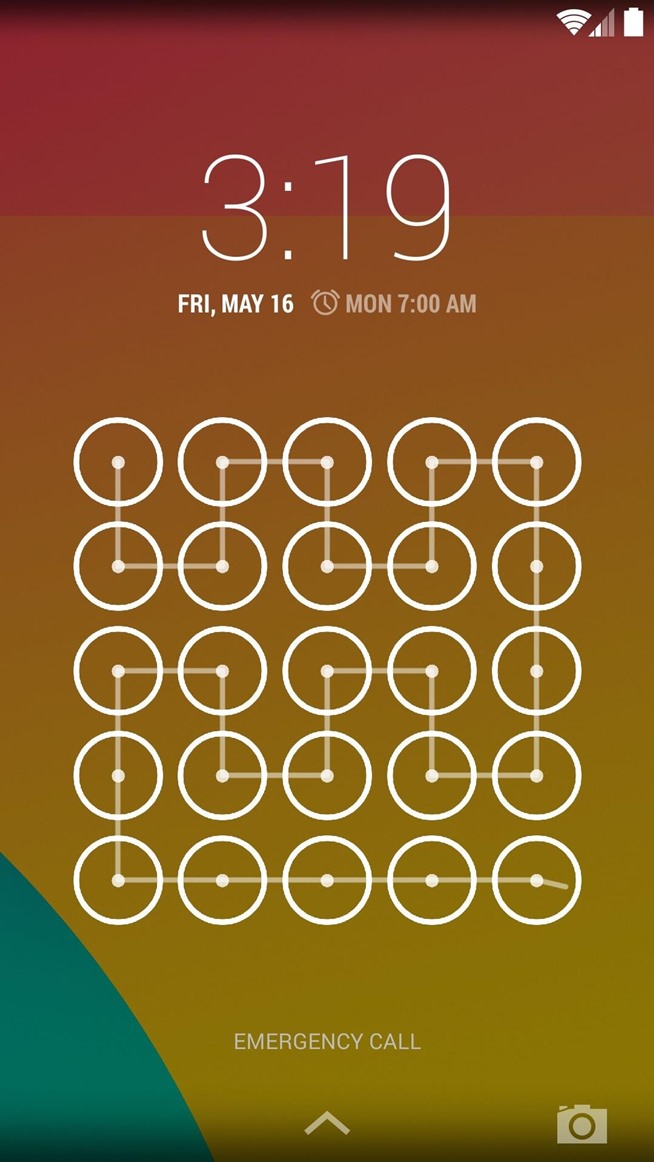
Of course, this headline can be a bit misleading. Only one conference attendee actually targeted Windows Phone. That man was Nico Joly, who targeted the Nokia Lumia 1520.
Joly targeted the browser and was able to exfiltrate the cookie database. However, the sandbox held strong and he was unable to gain full access to the system.
Joly’s partner in crime, Juri Aedla, attacked a Nexus 5 running Android via Wi-Fi. Despite his best efforts, he was unable to elevate his privileges beyond his original level.
A similar attack took place against a Samsung Galaxy S5, which was found to have “Samsung-specific flaws.” Those flaws allowed a Japanese team to target NFC as a vector to trigger a deserialization issue in certain code.
The iPhone 5S, on the other hand, was successfully hacked using a two-bug combination launched from within the Safari browser. That hacker, named lokihardt@ASRT, was able to perform a full Safari sandbox escape.
As for the prize money, hackers got way more than just bragging rights. Pwn2Own gives away as much as $300,000 for unknown zero day exploits in Android and iPhone. So if you’ve got the talent to seek out vulnerabilities and exploits, you can make a lot of money doing it.
You can read a full recap of Pwn2Own’s November 2014 event in Vancouver, British Columbia here.
