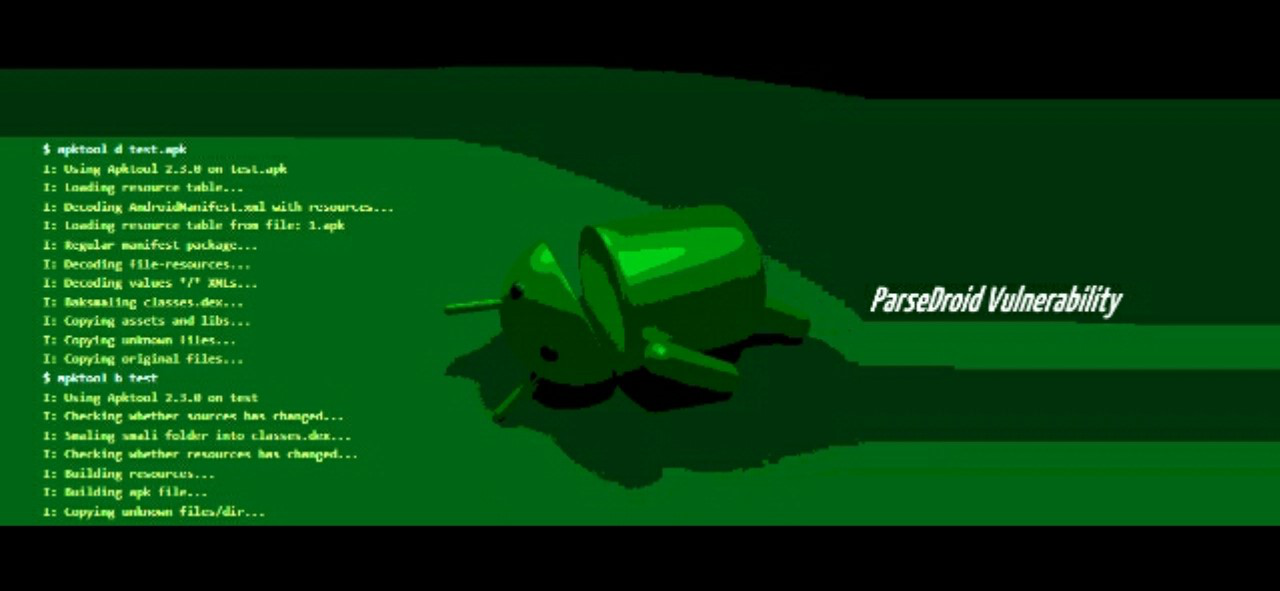
A new vulnerability has been found known as “ParseDroid”. This vulnerability affects development tools that are used by Android app developers which will allow hackers to steal files and execute some malicious code on the compromised machines.
Security researchers from an Israeli firm Check Point were the ones who discovered ParseDroid. It affects the XML parsing library filled with the projects like APKTool, IntelliJ, Eclipse as well as the Android Studio. Check Point security researchers found that the XML parsing library does not disable the external entity references when parsing an XML file – it’s a classic XEE or XML External Entity vulnerability which hackers can easily exploit.
It turns out that the attackers can also steal files from a computer that are running vulnerable IDEs. According to the researchers from Check Point:
“The vulnerability exposes the whole OS file system of [affected] users, and as a result, attackers could then potentially retrieve any file on the victim’s PC by using a malicious AndroidManifest.xml file.”
Since all Android applications have an AndroidManifest.xml file, it makes it easier for hackers to place and hide the malicious code in this file. Android app developers who use APKTool, Android Studio, Eclipse or IntelliJ to open an app which contains a malicious AndroidManifest.xml file is certainly at risk of having their files stolen by attackers. It goes without saying that all Android app developers and even security researchers who are using these tools to either compile or decompile Android APK files should update their IDEs.
Development teams are now well aware of this issue as Check Point has already notified them so that they can release updates to fix the ParseDroid flaw on all their affected products. It’s also worth mentioning that the APKTool is once again vulnerable to a second flaw. This second vulnerability allows attackers to execute their desired code on the compromised systems. This allows attackers in expanding their attack from blind data ex-filtration to an even more complex one which involves dropping more threatening malware on the targeted machines.
Exploiting the ParseDroid to attack Android app developers are easy to carry out as the malicious XML code can be hidden in plenty of places and not just in the AndroidManifest.xml file. For instance, the malicious code could also be hidden inside the Android Archive Library or AAR files.
Additionally, it’s a known fact that the Android development ecosystem is already used to cloning apps from different third-party websites. No wonder attacks will find it effortless to put on a malicious code which is under the guise of an open-source app template and libraries on GitHub as well as other repositories and get a hold of thousands of users without the need to dedicate lots of resources to ParseDroid attacks.
The ParseDroid vulnerability is also a cross-platform but which allows attackers to target app developers regardless of what operating system they are running. What’s alarming is that ParseDroid is silent as a mouse so its victims won’t be able to know that the attackers are stealing sensitive information or files from their infected systems.
A lot of Android app developers work for giant companies so it’s really a big threat and a big problem not just for the app developers but also for the companies they are working as the hacked systems could contain some closed-source code, intellectual property and trade secrets.
